Deployment Scenarios
Network Placement
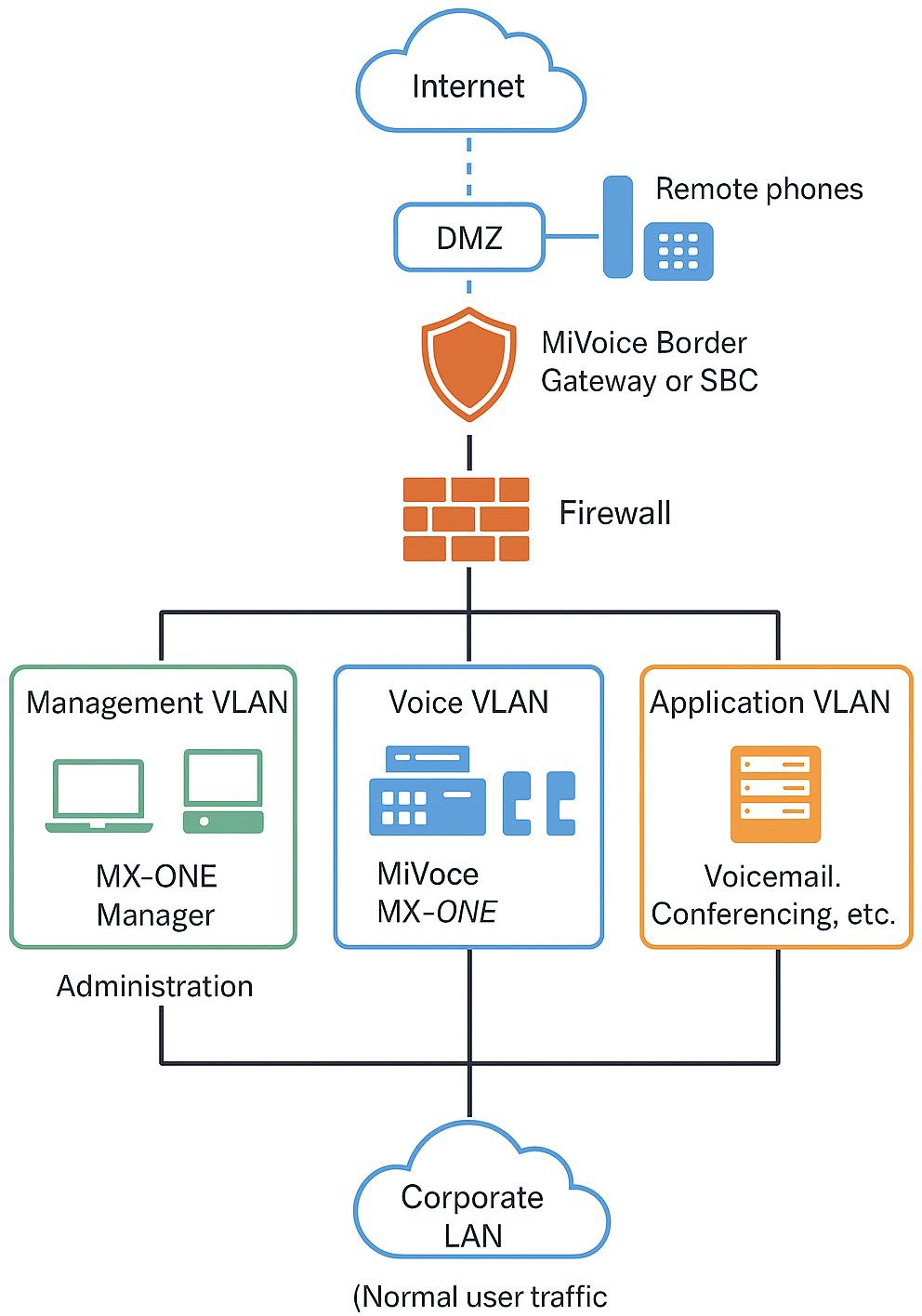
The MX-ONE platform, often used in large enterprise or carrier environments, supports both IP-based and traditional telephony. Its modular architecture comprising Media Gateways, Application Servers, Session Border Controllers (SBC), and Manager Tools demands a carefully planned network placement and layered security model.
Core Network Design
Split the deployment into logical zones using VLANs:
- Voice VLAN (for IP phones and SIP trunks)
- Management VLAN (for MX-ONE Manager, provisioning, SNMP, SSH)
- Application VLAN (for voicemail, conferencing, call recording)
- Corporate LAN (for normal user traffic)
Deploy dedicated Layer 3 segmentation and inter-VLAN firewalls to control cross-zone traffic.
DMZ Use (for External SIP Trunks or Remote Phones)
Deploy MiVoice Border Gateway (MBG) or third-party SBCs in the DMZ to handle:
- Remote extensions (Teleworker service)
- External SIP trunks
- WebRTC clients
PBX core (MX-ONE Service Node and Media Gateway) remains inside the trusted internal network.
IP Phone Placement
IP phones reside in the Voice VLAN, which:
- Is isolated from user LAN
- Is prioritized via QoS (DiffServ EF or 46) on all switches and routers
Virtual Deployments
For MX-ONE on VMware, Nutanix or Proxmox VE:
- Isolate virtual network interfaces per role (management, voice, public access)
- Use hardened hypervisor configurations and limit console access
Recommended Security Settings
- Permit SIP, H.248, and RTP only between:
- MBG/SBC ↔ MX-ONE Media Gateway
- IP phones ↔ MX-ONE
- Only allow management ports (HTTPS, SSH) from trusted IT admin subnets
- Disable unused services on all nodes, including legacy TFTP if not required
- Use Active Directory for centralized account control
- Enforce strong passwords for:
- Admin accounts on MX-ONE Manager
- SIP extension accounts (randomized credentials, ideally 12+ characters)
- Use Role-Based Access Control (RBAC) in the MX-ONE Manager Tool Suite
- TLS Encryption:
- Enable TLS for SIP signaling (SIP-TLS or SIPS)
- Use valid CA-signed certificates or an internal PKI
- SRTP:
- Enable SRTP for all supported phones and trunks
- Ensure end-to-end encryption from device to SBC or peer
- HTTPS for management interfaces only; disable HTTP
- Enable Intrusion Detection in MBG or SBC
- Rate-limit SIP registration attempts
- Geo-block untrusted countries if remote phones are used
- Fail2ban or equivalent on Linux-based manager nodes
- Set lockout thresholds for repeated failed login attempts
Monitoring, Logging & Compliance
- Enable SNMP and integrate with centralized monitoring (Zabbix, Nagios, or Mitel Performance Analytics)
- Forward logs to Syslog or SIEM for audit purposes:
- Call records (CDR)
Login attempts
Configuration changes
- Use MX-ONE Provisioning Manager for audit tracking of user/device modifications
- Retain logs for compliance per GDPR, HIPAA, or country-specific retention laws
Backup, Patching & Redundancy
- Schedule automated backups of:
- MX-ONE configuration
- Voicemail and call logs (if using Mitel CMG or MiCAM)
- Store backups off-system and validate restoration quarterly
- Keep all components Manager, Service Node, Media Gateways patched per Mitel's bulletins
- Enable clustering and redundancy:
- Dual-node configurations
- Hot standby for critical services (e.g., voice mail, SIP trunking)
Emergency Services & Regulatory Compliance
- Configure accurate location data (ELIN/ERL) for IP phones to ensure:
- Proper emergency call routing (e.g., 112, 911)
Support for E911 (via MBG or SIP trunk provider)
- Comply with:
- Lawful Intercept (if required)
- Call detail logging and retention policies